Trust-by-Design for Mobile Apps: Why Privacy and Security Can't Work in Silos
Mobile app risks sit at the intersection of privacy and security. Trust-by-Design brings both disciplines together — here's how.

This blog post is based on our white paper, Privacy and Security - The Friendship That Needs a Coffee Date
Trust-by-Design is showing up in consultancy decks and board presentations. The premise is simple: bake trust into operations from day one rather than bolting it on after something goes wrong.
But when it comes to mobile apps, the concept exposes a blind spot most organizations haven't addressed — the gap between privacy teams and security teams.
That gap is where mobile risks thrive.
The Mobile Risk Landscape
According to the OWASP Mobile Top 10 (2024), several of the most critical mobile application risks fall squarely at the intersection of privacy and security. Three stand out.
Inadequate Supply Chain Security in Mobile Apps
SDKs — Software Development Kits — are the building blocks of any modern app. They handle everything from analytics to payment processing to crash reporting. Ask your developers. They'll tell you how essential they are.
But SDKs are built by someone else, updated on their timeline, and can introduce vulnerabilities your team never signed off on. Each one represents third-party code running inside your app, expanding your attack surface and creating data flows you may not be aware of. They need continuous monitoring and assessment — not a one-time review at launch.
Inadequate Privacy Controls
Does your app conduct unnecessary or unlawful processing of personal data? Most apps handle some form of personally identifiable information (PII). Without adequate privacy controls to keep that processing lawful and proportionate, your organization risks violating both privacy regulations and information security standards. Clean data practices aren't optional. They're the baseline.
Insecure Data Storage: Where Breaches Begin
Weak encryption, insufficient data protection measures, and poor storage practices don't just put users at risk. They open the door to breaches that can expose your organization to regulatory action, financial loss, and lasting reputational damage. In some cases, the stored data itself becomes the weapon — enabling cyberattacks that could have been prevented with stronger development practices.
How Privacy and Security Teams Can Start Collaborating Today
To mitigate these risks effectively, privacy and security can't operate as parallel tracks. They need to work as one. Here are four areas where collaboration delivers immediate results.
Data Governance. Know what data you collect. Keep only what you need. Protect what you keep. These practices reduce the volume of mismanaged data across systems, which directly decreases the potential impact of a breach. This isn't just good practice — it's a core obligation under GDPR Article 5(1), and it maps to ISO 27001's information asset management controls and privacy-related controls (Annex A).
Vulnerability Handling. Privacy teams identify where sensitive data is exposed. Security teams implement the technical controls to close those gaps. This alignment reduces external exposure and supports compliance with vulnerability handling obligations under both GDPR Article 32 and NIS 2 Directive Article 21(2)(e).
Audit and Documentation. Privacy needs Records of Processing Activities (RoPA) and Data Protection Impact Assessments (DPIAs). Security needs logs, risk registers, and operational resilience documentation. When documentation is shared across teams, organizations reduce audit preparation costs and demonstrate transparency — to regulators, to partners, and to their own leadership.
Supply Chain and Third-Party Risk. Third-party risk assessments should integrate both privacy and security perspectives. Privacy teams evaluate whether processors handle personal data appropriately and conduct DPIAs. Security teams assess vendor security posture and technical dependencies. Together, red flags surface faster. This is also a direct requirement under NIS 2 Article 21(2)(d), which makes organizations responsible for the security of their supply chain — including the SDKs embedded in their apps.
How It All Comes Together: Trust-by-Design
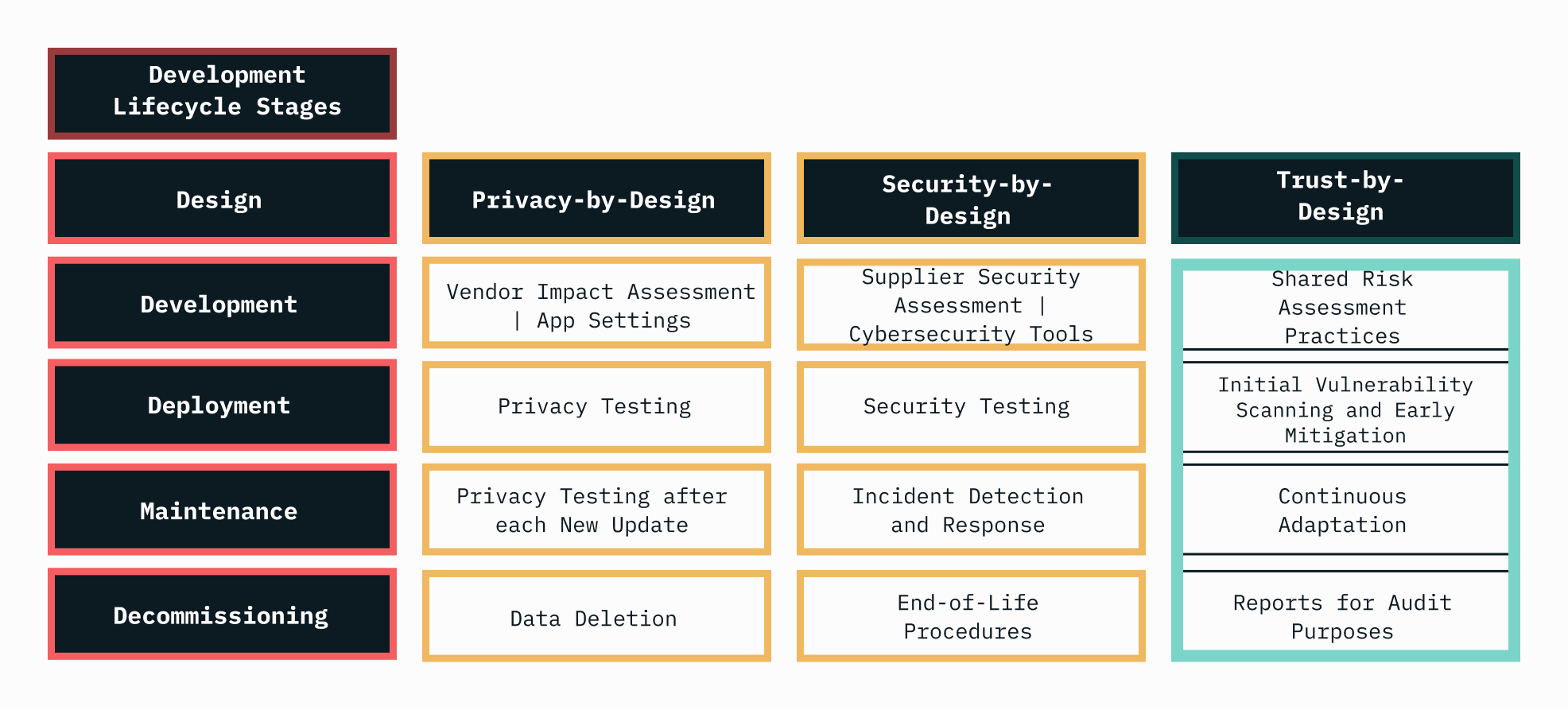
Trust-by-Design means embedding both privacy and security thinking into every stage of your app's lifecycle — from development through deployment to decommissioning. It's what happens when Privacy-by-Design and Security-by-Design stop running on parallel tracks and start sharing the same one.
Privacy-by-Design protects personal data. Security-by-Design protects systems and infrastructure. When both are woven into the development lifecycle, organizations don't just build compliant apps — they build transparent, end-to-end trust systems for both users and internal operations.
By identifying privacy-related threats during development, security teams gain better intelligence on where to implement robust technical measures. And by understanding the security implications of data flows, privacy teams can make more informed risk assessments.
Here's how the two disciplines complement each other across the application development lifecycle:
How Peak Privacy Helps You Achieve Trust-by-Design
Putting Trust-by-Design into practice requires visibility into what your apps actually do — not just what the documentation says they do. That's where automated, continuous auditing comes in.
Peak Privacy operationalizes Trust-by-Design for mobile environments. Our platform addresses the most pressing challenges in mobile data governance and digital risk management — especially around third-party code and regulatory compliance. It enables faster compliance work while breaking down the silos between privacy, security, and IT professionals.
Data Flow Detection. Our scanner autonomously downloads and tests each application the way a real user would — selecting the most privacy-protective settings available. It identifies unknown SDK transmissions and third-party endpoints that manual reviews miss.
Cross-Department Communication. The platform translates technical app behavior into regulatory language, breaking the silos between legal, security, and development teams. Reports give each stakeholder exactly what they need — without requiring compliance professionals to learn deep technicalities or developers to interpret legal frameworks.
Risk Mitigation Support. Peak Privacy enhances awareness and supports informed decision-making on development practices and supplier choices, reducing both privacy and security exposure.
Third-Party Risk Assessment. The platform surfaces insights into SDK suppliers and their data practices, supporting the supply chain security requirements under NIS 2 Article 21(2)(d) and ISO 27001 Annex A.5.19.
DPIA Support. Each app update triggers a new scan, automatically flagging new privacy risks and providing the evidence base for ongoing Data Protection Impact Assessments.
Audit Evidence. The platform documents how each app aligns with GDPR, ePrivacy, NIS 2, ISO 27001, and SOC 2 — giving you a compliance timeline that holds up under regulatory scrutiny.
Peak Privacy doesn't replace internal expertise — it enables collaboration where visibility is currently impossible.
Download the full white paper: "Privacy and Security – The Friendship That Needs a Coffee Date"
FAQ
- What is Trust-by-Design? Trust-by-Design is an operational approach based on a risk-based framework that combines Privacy-by-Design and Security-by-Design. For mobile apps, it means embedding both privacy and security considerations into every stage of the development lifecycle — from vendor selection to end-of-life procedures.
- How do privacy and security teams collaborate on mobile app compliance? The most effective collaboration happens in four areas: data governance, vulnerability handling, shared audit documentation, and joint third-party risk assessments. When both teams work from the same evidence base, organizations reduce compliance costs and close security gaps faster.
- Why are SDKs a supply chain risk? SDKs are third-party code libraries embedded in your app. Each one introduces code you didn't write, potentially expanding your attack surface and creating data flows outside your control. Under NIS 2 and ISO 27001, organizations are responsible for the security of their supply chain, and that includes the SDKs in their apps.
Also read:
CNIL's Mobile App Privacy Guidelines | Why France is scaling their app enforcement.